Darknet Markets 2026:
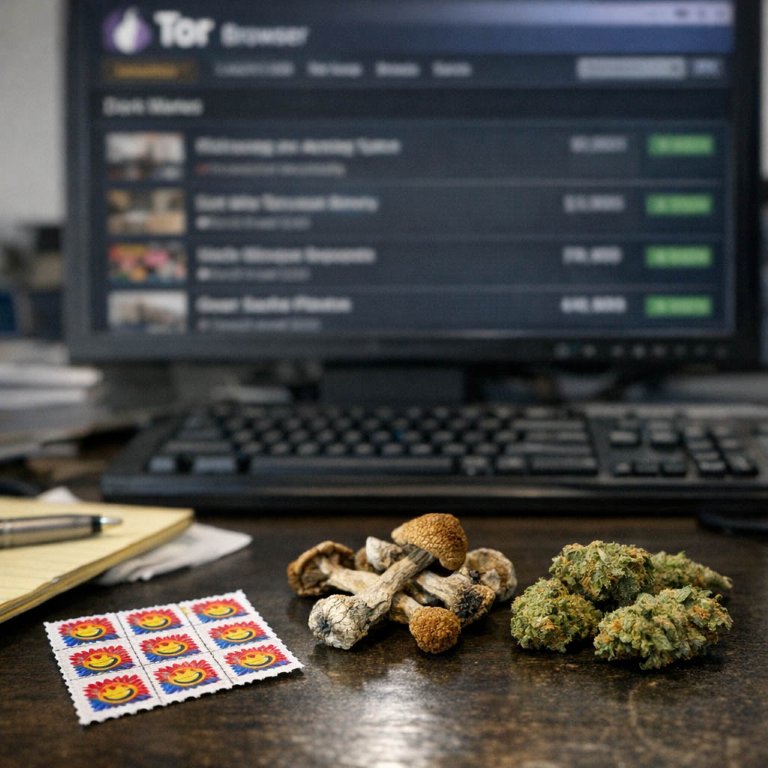
The dark web is part of the deep web but is built on darknets: overlay networks that sit on the internet but which can't be accessed without special tools or software like Tor. Tor is an anonymizing software tool that stands for The Onion Router — you can use the Tor network via Tor Browser.
| Darknet Market | Established | Total Listings | Link |
|---|---|---|---|
| Nexus Market | 2024 | 600+ | Onion Link |
| Abacus Market | 2022 | 100+ | Onion Link |
| Ares | 2026 | 100+ | Onion Link |
| Cocorico | 2023 | 110+ | Onion Link |
| BlackSprut | 2023 | 300+ | Onion Link |
| Mega | 2016 | 400+ | Onion Link |
Updated 2026-05-10
How to Find a Reliable Darknet for Your Needs
Finding the best darknet markets requires evaluating specific operational features that directly impact transaction success and user safety. The primary criteria focus on security architecture and vendor verification systems. A market's commitment to privacy is demonstrated by its mandatory use of PGP encryption for all communication and its implementation of a robust escrow service that holds cryptocurrency until the buyer confirms satisfactory receipt of the product.
Vendor reputation is the most reliable metric for assessing quality. Established markets maintain transparent feedback mechanisms where every transaction can be rated and reviewed. Shoppers should prioritize vendors with:
- A long-standing history on the platform
- A high number of completed sales
- Consistently positive reviews detailing product purity, stealth shipping methods, and reliable delivery times
Market stability is another critical factor. The most reputable platforms often employ invitation-only access or require a small entry fee to deter law enforcement and ensure a committed user base. While their URLs change frequently to mitigate DDoS attacks, they are reliably listed on major darknet market directories and forums. These directories provide updated .onion links and user commentary on a market's current operational status, which is essential for finding a stable and secure shopping environment.
How to Find a Good Darknet Market for Drugs
Finding the best darknet markets requires evaluating specific operational features that directly impact user success. A market's reputation is built on its vendor base and transaction security. Platforms hosting a high number of verified vendors with extensive transaction histories provide a more reliable environment. User reviews and forum feedback are critical for assessing vendor consistency and product quality.
Market architecture determines shopping security. Essential features include:
- A mandatory escrow service that holds payment until order completion.
- Support for multisignature (multisig) transactions as an additional layer of financial protection.
- End-to-end encrypted messaging systems between buyers and sellers.
- A clear and consistently enforced vendor bond policy, which acts as a financial barrier to entry for scammers.
Platform stability is another key factor. Established markets with longer uptime and consistent URL accessibility through reliable directories or invitation systems reduce the risk of loss. The most effective markets integrate these elementsverified vendors, enforced escrow, and robust operational securityinto a cohesive system that facilitates secure and efficient trade.
How to Safely Buy Drugs on the Darknet
Finding a suitable darknet market requires evaluating specific operational features that directly impact transaction success and user safety. The process is analytical, focusing on platform infrastructure and vendor reputation.
A market's longevity and stability are primary indicators. Established platforms with a consistent vendor base and a history of resolved transactions offer more reliability than frequently changing new entries. User reviews and forum discussions provide critical, crowdsourced data on a market's adherence to its own rules and its administrative responsiveness to disputes.
Vendor verification is a multi-layered analysis. Key elements to assess include:
- Verification badges or seniority status granted by the market administration.
- A long-term and consistent feedback history with detailed comments.
- Transparent shipping policies and standardized packaging methods.
- Clear communication practices and professional dispute resolution behavior.
Technical security features are non-negotiable. Essential features are end-to-end encryption for all messages, a robust escrow service managed by the platform until order completion, and support for anonymous cryptocurrencies like Monero. The absence of JavaScript and the presence of a valid PGP-signed deposit address are basic technical checks.
The most secure transactions occur when market infrastructure and verified vendor practices align. This combination creates a structured environment where regulated commerce can proceed with defined expectations for quality, delivery, and privacy.
How Reviews Help You Buy Safely on the Darknet
User reviews form the primary mechanism for establishing vendor reputation and market reliability. A high volume of positive feedback, particularly for completed transactions, directly indicates a vendor's consistency. Reviews detail product quality, shipping speed, and stealth packaging methods, providing a factual basis for selection beyond a simple product listing.
The review system allows for a decentralized form of verification. Customers report on the successful arrival of orders, which confirms the vendor's operational security and the market's functional escrow system. Dispute resolution outcomes are often visible, showing how the platform administers its internal policies. Patterns in negative reviews, such as complaints about product purity or communication failures, highlight specific risks.
Effective use of reviews involves analyzing their content over time. A vendor with a long history of positive transactions is generally a lower-risk choice. Newer vendors may offer competitive prices but carry inherent uncertainty. The collective intelligence found in review sections transforms individual experiences into a shared resource for secure shopping and identifying verified vendors.
How Escrow Makes Drknet Trading Safe and Fair
Escrow is the fundamental mechanism that enables trust in a drknet environment where direct trust between buyer and vendor is impractical. It functions as a neutral third-party service, typically managed by the market's automated system. When a buyer places an order, the funds are held in escrow and are not immediately released to the vendor. This creates a secure framework for the transaction to proceed.
The process follows a clear sequence:
1. The buyer sends payment to the market's escrow service.
2. The vendor is notified and ships the product.
3. Upon receipt, the buyer finalizes the order, releasing funds from escrow to the vendor.
This system protects both parties. For the buyer, it ensures payment is only released after confirming the product's arrival and quality, mitigating the risk of scams. For the honest vendor, it guarantees payment once the buyer is satisfied, as the funds are already secured and cannot be unilaterally withdrawn by the buyer. Disputes are handled by market moderators who review communication and evidence before deciding to release funds to either party. Reliable markets prioritize a robust and impartial escrow system, as it is the cornerstone of their reputation and long-term viability. Markets that abandon escrow in favor of direct payments, often labeled as "finalize early" or requiring excessive trust, present a significantly higher financial risk to the buyer.
How Darknet Markets Keep Drug Trade Safe and Private
The architecture of a leading darknet market is fundamentally engineered to facilitate secure and private transactions. This design begins with mandatory encryption. All communications, from vendor messaging to order details, are secured using PGP, ensuring that only the intended recipient can read the content. The market itself operates as a Tor hidden service, routing all traffic through multiple encrypted layers to anonymize user location and activity.
Financial privacy is maintained through the exclusive use of cryptocurrencies like Monero or Bitcoin. These currencies provide a layer of pseudonymity, with Monero offering enhanced privacy features that obscure transaction amounts and participant addresses. User accounts are designed to be ephemeral; no personal information is required for registration, and market operators have no means to access real-world identities.
The platform integrates a multi-signature escrow system as a core security feature. This system distributes control of funds between buyer, vendor, and market, requiring at least two parties to approve a transaction. This design significantly reduces the risk of exit scams by market administrators, as they cannot unilaterally seize coins held in escrow. The escrow process is automated and transparent within the platform's interface.
Operational security is reinforced by design choices that limit exposure:
- Automatic session timeouts and warnings against JavaScript.
- Internal messaging systems that never leave the encrypted environment.
- Vendor bond requirements that deter fraudulent sellers by imposing a financial cost to operate.
This comprehensive design creates a resilient environment where trade can proceed with a high degree of confidence in both privacy and transactional security, directly supporting the market's primary function.
How Link Changes Keep Darknet Markets Running Smoothly
The frequent rotation of darknet market URLs is a core feature of the ecosystem, not a bug. This dynamic change is a primary security and operational mechanism. Markets operate on a model of service availability rather than permanent location. The .onion address acts as a temporary access point.
Several factors drive this constant change:
- Proactive Security: Administrators voluntarily rotate URLs to preempt potential denial-of-service attacks or other targeting, maintaining platform stability.
- Domain Seizure Response: If a primary address is compromised, backup mirror links are activated to ensure business continuity and protect user funds in escrow.
- Traffic Management: Rotating links helps manage server load, distributing users across different nodes to ensure transaction speed and site performance.
For the user, this means the reliable darknet market is defined by its community reputation, vendor base, and escrow system, not by a single static URL. The most secure platforms integrate this link rotation into their design, communicating updates through verified channels like cryptographic signing of new addresses on clearnet forums or through private messaging systems. This process filters access to informed participants, enhancing overall network security by reducing exposure to random scanning and low-effort infiltration.
How Directories Keep You Connected to the Best Darknet Markets
Directories function as the primary clearinghouse for current darknet market URLs, aggregating verified links and operational statuses. These platforms are essential for navigating the frequent changes in market addresses caused by DDoS attacks and routine maintenance. A reliable directory provides more than a simple list; it offers user-submitted feedback on link functionality and often includes PGP-verified addresses to prevent phishing.
The utility of a directory is measured by its vetting process. Superior directories implement community-driven verification, where users confirm a link's legitimacy, and maintain a historical record of market uptime. This data allows for an analytical comparison of market stability. When assessing a directory, one should prioritize those that display:
- Real-time user reports on link status
- Integration of vendor forum announcements
- Clear timestamps for the last confirmed access
This ecosystem creates a self-correcting mechanism where outdated or fraudulent links are quickly identified and removed. The continuous update cycle ensures that the provided URLs have a high probability of granting access to the intended market, facilitating a more efficient connection to platforms known for secure escrow services and verified vendor profiles.
Secure Shopping with Invite-Only Darknet Markets
Invitation systems are a primary method for accessing the most reputable darknet markets. These private communities and invite-only forums function as a vetting mechanism, creating a barrier to entry that enhances overall security. The process filters out casual users and potential threats, cultivating a user base that is more committed to the principles of discreet and responsible trade. Gaining an invitation typically requires established trust within existing darknet circles, often demonstrated through a history of positive feedback on other platforms or contributions to related community discussions.
The markets accessible through these systems frequently offer superior features for secure shopping and vendor verification. They implement more robust multi-signature escrow options and encourage detailed user review systems. Vendor profiles in these spaces are often accompanied by extensive transaction histories and verifiable PGP keys, allowing for a more informed purchasing decision. The community within an invite-only market tends to be more active in self-policing, with users quickly reporting scams, which helps maintain a higher standard of reliability.
To find an invitation, one must engage with peripheral darknet resources. This involves consistent participation in dedicated clearnet forums and cryptocurrency discussion boards where trusted members occasionally distribute invites. Another effective strategy is to establish a positive trading record on a smaller, open-registration market first. A vendor with a good reputation there is more likely to receive an invitation to a larger, private platform. The key resources for this search include:
- Reputable darknet market directories that list which platforms are invite-only.
- Encrypted messaging channels associated with established darknet communities.
- Feedback sections of major markets, where users sometimes share information about newer, private alternatives.
This ecosystem ensures that the most secure shopping environments, with the highest concentration of verified vendors, remain protected by a layer of social verification. It directly links a user's reputation and effort to their access to higher-quality commercial spaces.