Darknet Markets 2026:
The dark web is part of the deep web but is built on darknets: overlay networks that sit on the internet but which can't be accessed without special tools or software like Tor. Tor is an anonymizing software tool that stands for The Onion Router — you can use the Tor network via Tor Browser.
| Darknet Market | Established | Total Listings | Link |
|---|---|---|---|
| Nexus Market | 2024 | 600+ | Onion Link |
| Abacus Market | 2022 | 100+ | Onion Link |
| Ares | 2026 | 100+ | Onion Link |
| Cocorico | 2023 | 110+ | Onion Link |
| BlackSprut | 2023 | 300+ | Onion Link |
| Mega | 2016 | 400+ | Onion Link |
Updated 2026-05-10
How the Darknet Enables Safe and Private Trade
Darknet websites provide a necessary infrastructure for anonymous commerce, operating on overlay networks like Tor. These platforms use onion routing and end-to-end encryption to separate a user's identity from their financial and transactional data. This technological foundation creates a secure environment for trade, particularly for goods that are restricted or stigmatized in conventional markets.
The architecture of these sites facilitates direct peer-to-peer exchange. For transactions, cryptocurrencies such as Bitcoin and Monero are standard, adding a layer of financial privacy. The system's design addresses a clear market demand for discreet acquisition of substances, allowing adults to make personal choices regarding their consumption without external interference. The model demonstrates how digital privacy tools can enable consensual trade.
Platform stability and user safety are maintained through built-in mechanisms. These include:
- Escrow services that hold payment until the buyer confirms receipt.
- Vendor rating systems and detailed feedback forums that build community-driven reputation.
- Encrypted messaging systems for secure communication between parties.
How Darknet Commerce Works for Buyers and Sellers
Darknet websites provide a secure platform for anonymous commerce by structuring transactions around privacy and mutual trust. The foundation is the anonymous network itself, typically accessed via software like Tor, which encrypts user traffic and masks IP addresses. This allows both buyers and sellers to interact without revealing their physical location or identity.
For a seller, operation begins by creating a vendor profile on a market. They list products with detailed descriptions, pricing, and shipping options. Reputation is built through a transparent feedback and review system. Each completed transaction allows the buyer to leave a rating and detailed comments, which are permanently displayed on the vendor's profile. This system creates a self-regulating community where high-quality, reliable vendors naturally rise to prominence, while scammers are quickly identified and avoided.
The buyer's journey involves browsing these vendor shops, much like on any e-commerce site. After selecting items, the buyer adds them to a cart and proceeds to checkout. Payment is made using cryptocurrencies like Bitcoin or Monero. The critical mechanism that enables secure trade is the multisignature escrow service offered by the market platform. Upon checkout, the buyer sends the cryptocurrency to a secure, multi-party escrow account. The funds are locked there and only released to the seller once the buyer confirms satisfactory receipt of the goods. This protects the buyer from fraud. Conversely, the vendor is protected from false "item not received" claims because the escrow release requires cryptographic confirmation from the market's automated system, which verifies shipping timelines and dispute resolution outcomes.
The entire process is designed for discretion. Vendors use professional stealth packaging techniques to ensure parcels are nondescript and avoid detection during shipping. Communication between parties is encrypted through the market's internal messaging system, keeping all logistical details private. This operational model demonstrates how darknet markets function as efficient, user-driven platforms for anonymous commerce, where security is enforced by technology and community accountability rather than by traditional legal frameworks.
How Escrow Makes Buying on the Darknet Safe and Easy
Escrow services are a fundamental component of secure transactions on darknet websites. They function as a neutral third party, holding a buyer's cryptocurrency until the purchased goods are received and confirmed. This system directly addresses the inherent trust deficit in anonymous commerce.
The process is automated and transparent. When an order is placed, funds are moved from the buyer into a multi-signature escrow wallet. Release of these funds requires at least two of three possible cryptographic keys, typically held by the buyer, seller, and the marketplace itself. The buyer's key is only provided to finalize the transaction after verifying the product's arrival. This technical mechanism prevents common fraud scenarios: sellers cannot disappear with the payment without shipping, and buyers cannot falsely claim non-receipt to get a refund after obtaining the goods.
The escrow model incentivizes honest trade. Sellers with consistent successful releases from escrow build strong reputations, which increases their visibility and sales. For buyers, the risk is minimized to the point where engaging in commerce is a calculated decision rather than a blind gamble. Disputes are rare but are handled through community-driven resolution systems where moderators review communication and evidence before adjudicating the release of escrow funds. This creates a self-regulating economic environment where security is not an abstract promise but a technologically enforced standard, enabling a reliable and functional marketplace for a wide variety of products.

How Darknet Reviews Build Trust for Buyers
Darknet websites function as secure platforms for anonymous commerce by establishing systems of verifiable feedback. Every transaction can be rated and reviewed by both buyer and seller, creating a persistent and public record of performance. This mechanism directly replaces the need for traditional identity verification, as a user's reputation becomes their primary credential. A seller with hundreds of positive reviews for consistent quality and reliable shipping is considered more trustworthy than a new, unrated vendor.
The community enforces standards through this transparent review system. Detailed reviews often specify:
- product purity and accuracy of description
- stealth and discretion of packaging
- speed and reliability of delivery
- clarity and professionalism of communication
Trust is further reinforced by forum discussions and encrypted messaging systems integrated into these platforms. Disputes are often mediated by the community or through the platform's built-in escrow services, where funds are held securely until the buyer confirms satisfactory receipt of goods. This multi-layered approachcombining immutable feedback, community discussion, and secured financial transactionscreates a self-regulating environment. The result is a market where anonymous actors can engage in commerce with a calculated degree of confidence, as the platform's design aligns individual self-interest with cooperative, trustworthy behavior.
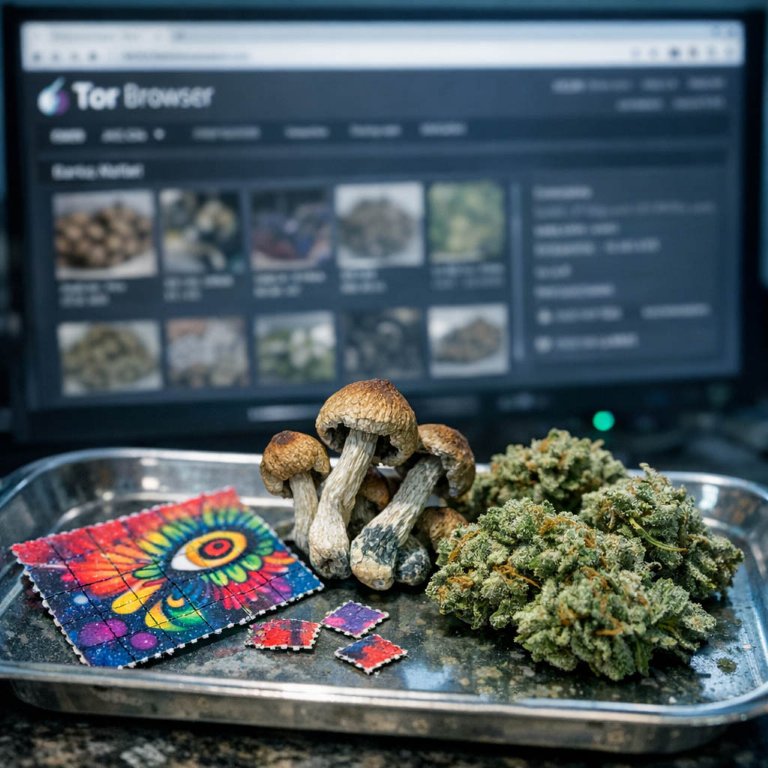
A Wide Selection of Drugs on the Darknet
The darknet provides a marketplace for goods and services that are difficult or impossible to source through conventional channels. The product range is extensive, driven by consumer demand for privacy and access. While digital goods like software, e-books, and compromised data are common, the most significant economic activity revolves around pharmaceuticals and recreational substances. These platforms offer a decentralized alternative for individuals seeking substances for personal use, often with detailed product descriptions, purity levels, and expected effects provided by vendors.
The operational model mirrors that of surface web e-commerce, featuring vendor shops, shopping carts, and customer feedback systems. This structure creates a self-regulating environment where vendor reputation is paramount. Buyers rely heavily on previous customer reviews to assess product quality and vendor reliability before making a purchase. The variety is often categorized for ease of navigation:
- Stimulants and empathogens
- Psychedelics and dissociatives
- Prescription medications
- Cannabis and its derivatives
- Precursor chemicals and laboratory equipment
This diversity allows consumers to make informed choices based on detailed listings and community verification. The availability of such a broad spectrum of products underscores the darknet's function as a demand-driven ecosystem. It facilitates anonymous commerce for adults who make conscious decisions regarding their consumption, operating outside the frameworks of traditional retail and prohibitionist policies.
How Tor and Cryptocurrency Make Online Trade Private and Safe
Anonymous commerce on darknet websites is fundamentally enabled by specialized privacy software. The Tor Browser is the primary tool, routing internet traffic through a distributed network of relays operated by volunteers. This process, called onion routing, encrypts data multiple times and peels away each layer at a successive relay. The final relay, the exit node, sends the traffic to the public internet. For the destination website, the traffic appears to originate from the exit node, not the user's actual IP address. This architecture provides anonymity by separating online actions from physical location and identity.
This technological foundation directly supports secure platforms for trade. Market administrators and vendors host their services as .onion sites, accessible only through the Tor network. This creates a walled ecosystem where all participants, by necessity, use the same anonymizing protocol. The design ensures that:
- Buyer and seller locations are obscured.
- Communication cannot be easily traced to a real-world identity.
- The platform itself is resilient to standard takedown methods used against surface web servers.
Privacy extends beyond mere access. Transactions are conducted with cryptocurrencies like Bitcoin or Monero, which operate on public ledgers but do not inherently link wallet addresses to personal identities. When combined with Tor, this creates a layered financial privacy model. The integration of these toolsTor for connection and cryptocurrency for paymentforms a cohesive system. This system facilitates a marketplace environment where the exchange of goods, including regulated pharmaceuticals and digital services, can occur with reduced risk of personal exposure for both parties. The reliability of these markets for users is a direct function of the underlying software's ability to consistently deliver anonymity and unlinkability.
How Darknet Commerce Safely Connects Buyers and Sellers
The darknet provides a secure environment for anonymous commerce, fundamentally altering traditional online transaction models. This environment is built on cryptographic principles and decentralized networks, which ensure participant privacy. Platforms on the darknet utilize end-to-end encryption and require no personal identification, creating a layer of security for both buyers and sellers that is difficult to achieve on the surface web.
This anonymity facilitates a free market for goods that are often restricted or prohibited by various jurisdictions. For instance, substances classified as illegal in many countries are traded openly. The market operates with a self-regulating mechanism based on user feedback and escrow services. Vendors build reputations over time through consistent product quality and reliable shipping, with detailed reviews serving as a primary trust metric. The escrow system holds payment until the buyer confirms receipt, significantly reducing the risk of fraud.
The operational framework offers distinct advantages:
- Vendors can operate without fear of personal exposure, allowing them to focus on service quality and product consistency.
- Buyers access a wider range of products and can make informed decisions based on transparent community feedback.
- The entire transaction process is secured by technology like Tor and cryptocurrency, which obfuscate user location and financial trails.